Tag: infosecurity
7 Top Cybersecurity Trends in 2019

The PKI Guy discusses digital certificates security with Muralidharan Palanisamy of AppViewX

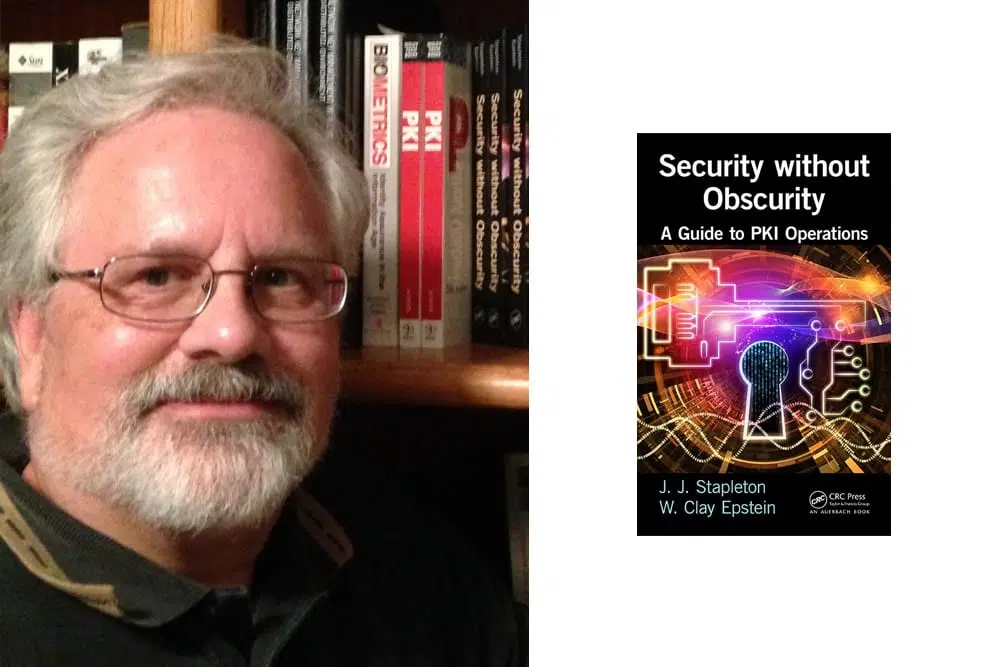
The PKI Guy drills down on PKI operations with Jeff Stapleton, author
The PKI Guy explores data encryption with Cindy Provin of nCipher Security

